Set up SSL Certificates on Android, and instantly, your digital life positive aspects a layer of armor! Think about a world the place your delicate info, from banking particulars to non-public emails, is shielded from prying eyes. This is not a futuristic fantasy; it is the truth enabled by SSL certificates. We’ll embark on a journey to know these digital guardians, exploring how they safeguard your knowledge and why they’re important for anybody navigating the web panorama with an Android system.
From understanding the core ideas of SSL/TLS to the sensible steps of set up, we’ll traverse the terrain of certificates codecs, troubleshoot widespread hiccups, and uncover the very best practices for a safe cell expertise. We’ll delve into the nuances of certificates revocation, the significance of trusted sources, and the artwork of managing these digital keys with utmost care. Put together to rework your Android system right into a fortress of privateness and safety.
Understanding SSL Certificates and Android: Set up Ssl Certificates On Android

Hey there, tech lovers! Ever puzzled how your Android system retains your knowledge protected once you’re looking the online or utilizing apps? Nicely, an enormous a part of that safety comes right down to one thing known as SSL certificates. Let’s dive in and unravel this fascinating world, ensuring you are well-equipped to navigate the digital panorama with confidence.
What’s an SSL Certificates and Its Operate in Securing Knowledge Transmission
An SSL (Safe Sockets Layer) certificates, or its extra fashionable successor, TLS (Transport Layer Safety), is basically a digital passport that verifies a web site’s identification. Consider it like a badge of belief that confirms a web site is who it claims to be. Its main operate is to encrypt the information transmitted between your Android system and the web site’s server.
This encryption scrambles the knowledge, making it unreadable to anybody who may attempt to intercept it, like a secret code solely the meant events can decipher.This is the way it works:
- Authentication: The certificates proves the web site’s authenticity. When your Android system connects to a web site, the server presents its SSL certificates. Your system checks the certificates to make sure it is legitimate and issued by a trusted Certificates Authority (CA).
- Encryption: As soon as the certificates is verified, your system and the server set up a safe, encrypted connection. This implies all knowledge exchanged between them, like passwords, bank card particulars, and private info, is scrambled, stopping eavesdropping.
- Knowledge Integrity: The certificates ensures that the information hasn’t been tampered with throughout transmission. If any knowledge is altered, the encryption will fail, alerting the consumer to a possible safety breach.
Think about this:
SSL certificates create a safe tunnel for knowledge, making certain confidentiality, integrity, and authenticity.
Examples of Situations The place SSL Certificates are Essential for Android Customers
SSL certificates are important for safeguarding your knowledge in quite a few eventualities in your Android system. Listed below are just a few key examples:
- On-line Banking: Once you entry your financial institution’s web site or cell app, an SSL certificates encrypts your login credentials and monetary transactions, defending your cash and private info from cybercriminals. Think about the chaos in case your banking particulars have been intercepted!
- E-commerce: Procuring on-line is considerably safer due to SSL certificates. They encrypt your bank card info, delivery handle, and different delicate particulars throughout the checkout course of. With out this safety, your knowledge could possibly be weak to theft, resulting in monetary loss and identification theft.
- E mail Communication: Safe electronic mail suppliers use SSL certificates to encrypt your emails, making certain that your personal messages stay confidential. This prevents unauthorized entry to your private {and professional} communications.
- Social Media: Once you log into social media platforms, SSL certificates defend your username, password, and different private info from being intercepted. This safeguards your account from being hacked and your knowledge from being misused.
- Net Shopping: Everytime you browse the online, SSL certificates are at work, securing your connection to web sites. This ensures that the knowledge you alternate with web sites, akin to search queries, type submissions, and looking historical past, stays personal. Search for the “https” within the handle bar and the padlock icon to know if a web site is utilizing SSL.
Take into consideration the sheer quantity of delicate info we deal with on our Android gadgets day by day. With out SSL certificates, all of this knowledge can be uncovered to potential threats.
Variations Between SSL, TLS, and Their Relationship to Certificates Safety
Whereas the phrases SSL and TLS are sometimes used interchangeably, it is essential to know their relationship. SSL is the older protocol, whereas TLS is its safer and superior successor. Each are cryptographic protocols designed to supply safe communication over a community.This is a breakdown:
- SSL (Safe Sockets Layer): SSL was the unique protocol, developed within the mid-Nineties. It was designed to ascertain a safe connection between an internet browser and an internet server. Nonetheless, because of a number of vulnerabilities and safety flaws, SSL is now thought of out of date and is not really helpful to be used.
- TLS (Transport Layer Safety): TLS is the successor to SSL. It is a safer and strong protocol that addresses the vulnerabilities of SSL. TLS supplies stronger encryption algorithms, improved key alternate mechanisms, and higher safety in opposition to numerous assaults. TLS is the usual protocol used at this time for securing on-line communications.
- Relationship: TLS is basically an up to date and improved model of SSL. Consider it like this: SSL is the older mannequin, and TLS is the newer, extra superior model with higher options and safety. Once you see “SSL” talked about in fashionable contexts, it usually refers to TLS, as TLS has successfully changed SSL.
- Certificates Safety: Each SSL and TLS depend on digital certificates to confirm the identification of internet sites and encrypt knowledge. The certificates themselves are the identical for each protocols. The distinction lies within the underlying protocols used to ascertain and preserve the safe connection. As a result of TLS is safer, utilizing a TLS-enabled web site supplies higher safety.
Think about the evolution of know-how:
SSL paved the way in which, however TLS is the present champion in making certain safe on-line interactions.
Getting ready Your Android System
Earlier than you dive into putting in an SSL certificates in your Android system, it is important to get your digital geese in a row. Consider it like making ready your workspace earlier than beginning a fancy challenge – a tidy setup results in smoother crusing. This part Artikels the important steps to prepared your Android system for the certificates set up course of, making certain a safe and hassle-free expertise.
Crucial Steps for Preparation
To make sure a clean certificates set up, just a few preliminary steps are essential. These steps lay the groundwork for a safe and useful implementation.First, guarantee your Android system is up to date to the newest accessible working system model. Software program updates usually embody essential safety patches that handle vulnerabilities. You may examine for updates in your system’s settings below “System” or “About Cellphone,” then “Software program Replace.” The method usually entails downloading and putting in the replace, adopted by a tool restart.Subsequent, you could purchase the SSL certificates in a format appropriate with Android, usually a `.crt` or `.pem` file.
This file incorporates the general public key and different important details about the certificates. You will receive this file out of your Certificates Authority (CA) or the supply offering the certificates. Guarantee you’ve gotten entry to the file in your system, both by downloading it instantly or transferring it from one other system or laptop.Lastly, contemplate the community connection. A secure and dependable web connection is significant throughout the set up course of.
Guarantee your system is related to a Wi-Fi community or has a powerful mobile knowledge sign. This may stop interruptions throughout the certificates import and validation steps.
Checking the Present Belief Retailer
Understanding your system’s current belief retailer is essential earlier than including a brand new certificates. This belief retailer is basically a set of pre-installed certificates from trusted Certificates Authorities (CAs). Checking the present state helps keep away from conflicts and ensures the brand new certificates integrates appropriately.Accessing the belief retailer instantly on most Android gadgets is just not easy. Nonetheless, you’ll be able to confirm if a selected certificates is already trusted by making an attempt to entry a web site that makes use of that certificates.
If the web site masses with none safety warnings, the certificates (or the CA that signed it) is probably going already trusted. Conversely, in the event you obtain a warning about an untrusted connection, the certificates is just not presently acknowledged.One other technique entails utilizing a third-party software designed for managing and inspecting certificates. A number of apps accessible on the Google Play Retailer permit you to view the contents of the belief retailer, together with the put in certificates and their particulars.
Use warning when putting in such purposes and guarantee they arrive from respected sources.It is also potential to make use of command-line instruments in case your system is rooted or you probably have entry to the Android Debug Bridge (ADB). ADB permits you to work together along with your system from a pc. Utilizing ADB, you’ll be able to extract the belief retailer information and look at their contents. Nonetheless, this technique is extra technical and requires superior data.
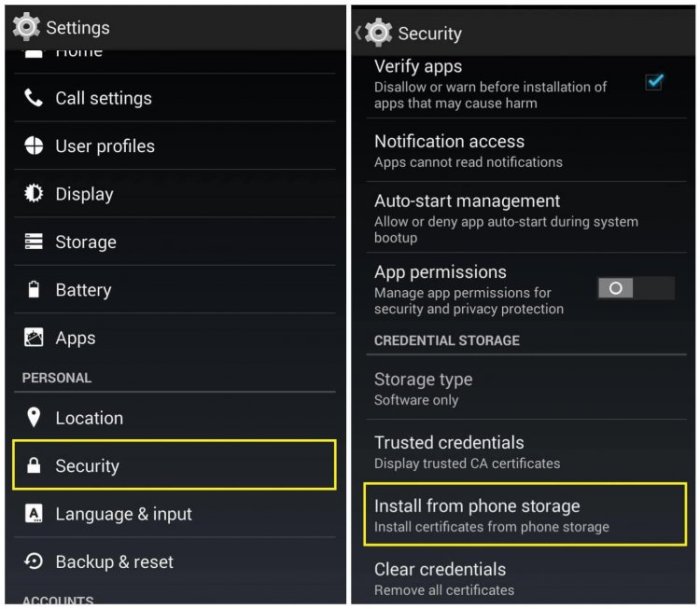
Settings and Permissions
Earlier than putting in a certificates, particular settings and permissions should be in place. These configurations assure the certificates is appropriately built-in and features as meant.First, you may must allow the flexibility to put in certificates from exterior sources. Navigate to your system’s settings, normally below “Safety” or “Privateness.” Search for an possibility associated to “Set up from storage” or “Set up certificates.” You may must grant the browser or file supervisor you may use to entry the certificates file the required permissions.
The precise wording and placement of those settings might range barely relying in your Android model and system producer.Subsequent, contemplate the community settings. When you plan to make use of the certificates for a selected Wi-Fi community, you may must configure the community settings to belief the certificates. Go to the Wi-Fi settings, choose the community, and search for choices associated to “Proxy,” “CA certificates,” or “Safety.” Right here, you may specify the certificates file and configure the required settings.Lastly, guarantee you’ve gotten the right permissions for the certificates file itself.
The file must be accessible out of your system’s storage. You might must grant permission to the file supervisor or browser you are utilizing to entry the file. If you’re transferring the certificates from a pc, make certain the file switch is full and that the file is just not corrupted.
Strategies for Putting in SSL Certificates
Securing your Android system with an SSL certificates is essential for safeguarding your knowledge and making certain safe communication. Happily, Android affords a number of strategies for putting in these certificates, every with its personal benefits and concerns. Selecting the best technique is dependent upon your particular wants and the kind of certificates you are utilizing. Let’s delve into the varied methods you’ll be able to fortify your system’s safety.
Putting in a Certificates through System Settings
One of the easy strategies for putting in an SSL certificates in your Android system is thru the system’s settings menu. This method is usually appropriate for putting in consumer certificates, usually used for authenticating to inside networks or particular purposes.Right here’s a step-by-step process:
- Get hold of the Certificates File: Guarantee you’ve gotten the certificates file in a format supported by Android, usually
.crt,.cer, or.pem. - Switch the Certificates: Switch the certificates file to your Android system. You are able to do this through USB, Bluetooth, electronic mail, or a cloud storage service.
- Entry Safety Settings: Open your system’s Settings app. Navigate to the “Safety” or “Safety & Location” part. The precise wording might range relying in your Android model and system producer.
- Discover Certificates Settings: Inside the Safety settings, search for an possibility associated to “Encryption,” “Credentials,” or “Certificates.” Faucet on this feature.
- Set up a Certificates: It’s best to see an choice to “Set up a certificates” or “Set up from storage.” Faucet on this feature. You might be prompted to enter your system’s PIN, password, or sample for safety.
- Choose the Certificates: Browse your system’s storage and choose the certificates file you transferred earlier.
- Title the Certificates: You’ll possible be prompted to present the certificates a reputation. This helps you establish it later.
- Select Certificates Utilization: Choose how the certificates will likely be used (e.g., for Wi-Fi or VPN).
- Belief the Certificates: Relying in your system, you is likely to be requested to belief the certificates. Be sure to perceive the implications earlier than trusting it.
- Verification: As soon as put in, you’ll be able to usually view the put in certificates within the “Trusted credentials” or “Person credentials” part of your safety settings.
You will need to perceive that the exact steps can range barely relying in your Android model and the producer of your system (Samsung, Google Pixel, and many others.). Nonetheless, the overall course of stays constant.
Putting in a Certificates Utilizing a File Supervisor
One other technique for putting in SSL certificates entails utilizing a file supervisor software in your Android system. This generally is a helpful different, particularly if the direct set up technique through settings is not working as anticipated or in the event you choose a extra hands-on method. This method is especially useful once you want extra management over the certificates set up course of.Right here’s how one can do it:
- Get a File Supervisor: When you do not have already got one, obtain and set up a file supervisor app from the Google Play Retailer. Well-liked decisions embody Recordsdata by Google, Strong Explorer, or ES File Explorer (although be conscious of potential privateness considerations with some third-party apps).
- Get hold of the Certificates File: Guarantee you’ve gotten the certificates file (
.crt,.cer, or.pem) in your system. - Find the Certificates: Use the file supervisor to navigate to the placement the place you saved the certificates file.
- Choose the Certificates: Faucet on the certificates file to pick out it.
- Select “Set up”: The file supervisor ought to supply an “Set up” or “Open with” possibility. Choose “Set up” (or select an possibility that installs certificates).
- Observe the Prompts: The set up course of will then information you thru the identical steps because the settings technique, together with offering a reputation, deciding on utilization, and confirming belief. You is likely to be redirected to the system settings to finish the method.
- Verification: As with the settings technique, you’ll be able to confirm the set up by checking the “Trusted credentials” or “Person credentials” part in your system’s safety settings.
Utilizing a file supervisor offers you extra management over the file choice course of and may typically bypass limitations or points you may encounter with the system settings technique.
Comparability of Set up Strategies
To summarize the totally different set up strategies and their respective professionals and cons, here’s a comparative desk. This may provide help to select the very best method primarily based in your particular wants and state of affairs.
| Technique | Execs | Cons |
|---|---|---|
| System Settings |
|
|
| File Supervisor |
|
|
Putting in Certificates for Particular Apps
Typically, you do not want or wish to set up a certificates system-wide in your Android system. Maybe you solely must belief a certificates for a selected app or net browser, like when testing a improvement setting or accessing a secured inside service. This method affords extra granular management, minimizing the potential safety influence of a misconfigured certificates.
Configuring Firefox or Chrome to Belief a Customized SSL Certificates
Net browsers like Firefox and Chrome on Android supply methods to belief customized SSL certificates, permitting safe connections to web sites that use self-signed certificates or certificates issued by a personal Certificates Authority (CA). The method differs barely between the 2 browsers.For Firefox:
- Open Firefox in your Android system.
- Navigate to the web site utilizing the customized certificates. Firefox ought to show a warning indicating an untrusted connection.
- Faucet on the lock icon within the handle bar.
- Choose “View Certificates.”
- Faucet on the “Particulars” tab.
- You will see details about the certificates, together with the issuer.
- You may’t instantly “set up” the certificates in Firefox like you’ll be able to in some desktop variations. As a substitute, Firefox depends on the Android system’s trusted certificates retailer, or requires you so as to add an exception for the particular website. If the CA that signed your certificates is already trusted by Android, Firefox will mechanically belief the web site. If not, you will notice the warning.
You may select to proceed regardless of the warning, successfully trusting the certificates for that particular web site.
- Be extraordinarily cautious when bypassing safety warnings. Make sure you perceive the dangers related to trusting a certificates earlier than continuing. This method is usually appropriate for improvement and testing environments, however must be fastidiously thought of for manufacturing environments.
For Chrome:
- Chrome on Android primarily makes use of the Android system’s certificates retailer. If the certificates’s CA is trusted by the Android system, Chrome will mechanically belief web sites utilizing that certificates.
- If the certificates is just not trusted by the Android system, Chrome will show a warning. In contrast to Firefox, Chrome does not supply a direct solution to bypass this warning or set up a certificates particularly for the browser.
- The very best method for Chrome is to make sure the certificates’s CA is trusted on the Android system degree.
- To do that, you would wish to put in the CA certificates as described within the system-wide set up strategies.
- Alternatively, in the event you’re utilizing Chrome for improvement or testing, think about using a publicly trusted certificates or configuring your improvement server to make use of a trusted certificates authority. This avoids the necessity to set up a customized CA certificates in your system.
Configuring a Proxy Server with an SSL Certificates on an Android System
Establishing a proxy server in your Android system, significantly one which makes use of SSL encryption, permits you to monitor and filter community site visitors. This may be useful for debugging, safety testing, and content material filtering. The setup entails configuring the proxy server and configuring your Android system to make use of the proxy.To configure a proxy server, you usually want the next:
- A proxy server software: Well-liked decisions embody instruments like Burp Suite, Charles Proxy, or Fiddler. These instruments can act as a “man-in-the-middle” (MITM) proxy, permitting you to intercept and examine HTTPS site visitors.
- A certificates for the proxy server: These proxy instruments usually generate their very own SSL certificates. You will want to put in the proxy server’s CA certificates in your Android system to belief the proxy’s connections.
- Android system configuration: You must configure your Android system to make use of the proxy server. This usually entails coming into the proxy server’s IP handle and port quantity in your Wi-Fi community settings.
This is a step-by-step information:
- Set up the Proxy Server: Obtain and set up your chosen proxy server software in your laptop.
- Generate and Configure the Proxy’s SSL Certificates: The proxy server will generate an SSL certificates. Typically, you will have to:
- Discover the certificates file (normally a .cer or .pem file) generated by the proxy.
- Export the certificates in a format appropriate with Android (normally DER or PEM).
- Some proxy instruments might mechanically generate and set up the certificates into the right keystore in your system, simplifying this step.
- Set up the Certificates on Your Android System: As described within the earlier sections, set up the proxy server’s CA certificates in your Android system. This makes your system belief the proxy server’s connections.
- Configure Your Android System to Use the Proxy:
- Go to your Android system’s Wi-Fi settings.
- Discover the Wi-Fi community you might be related to and faucet on it.
- Search for the “Proxy” settings.
- Choose “Guide” or the same possibility.
- Enter the proxy server’s IP handle and port quantity. You may normally discover this info within the proxy server software’s settings.
- Save the settings.
- Check the Connection: Browse the web in your Android system. If every little thing is configured appropriately, your site visitors will likely be routed by way of the proxy server. It’s best to be capable of see the requests and responses within the proxy server software.
Do not forget that utilizing a proxy server, particularly one which intercepts encrypted site visitors, can have safety implications. Solely use proxy servers from trusted sources and make sure you perceive the dangers concerned. Additionally, guarantee you might be licensed to intercept the site visitors.
Troubleshooting Widespread Points
Putting in SSL certificates on Android, whereas usually easy, can typically really feel like navigating a maze. Numerous roadblocks can seem, from cryptic error messages to surprising app conduct. However worry not! This part will equip you with the data to beat these challenges, reworking potential complications into manageable duties.
Certificates Not Trusted Errors
The dreaded “certificates not trusted” error is a standard foe. It usually alerts that your Android system does not acknowledge the certificates authority (CA) that issued the SSL certificates. Consider it as your cellphone saying, “I do not know this man; is he legit?” A number of elements can set off this mistrust, and understanding them is step one towards decision.When a certificates is untrusted, the Android system prevents safe connections, probably blocking entry to web sites or apps that depend on that certificates.
This can be a essential safety measure designed to guard consumer knowledge. Nonetheless, in sure instances, akin to when coping with self-signed certificates or certificates from less-known CAs, this safety characteristic can develop into an impediment.This is a breakdown of widespread causes and options:
- The CA is just not within the Android’s Belief Retailer: Android gadgets include a pre-installed record of trusted CAs. If the CA that issued your certificates is not on this record, your system will not belief the certificates.
- Answer: Set up the CA’s root certificates in your system. This provides the CA to the belief retailer, permitting your system to acknowledge and belief certificates issued by that CA. This course of normally entails downloading the basis certificates (usually a .crt or .pem file) and importing it by way of the system’s settings.
- The Certificates Has Expired: SSL certificates have an outlined lifespan. As soon as the certificates expires, it is not legitimate, and your system will refuse to belief it.
- Answer: Renew the certificates earlier than it expires and reinstall the up to date certificates in your system. Most CAs present reminders about certificates expiration, making it simpler to remain forward of this difficulty.
- Incorrect Certificates Chain: An SSL certificates is usually a part of a sequence, together with the end-entity certificates (the one on your web site or app) and intermediate certificates that hyperlink again to a trusted root CA. If the chain is incomplete or improperly configured, the system might not be capable of confirm the certificates’s authenticity.
- Answer: Be sure that the whole certificates chain is appropriately put in on the server the place the certificates is getting used.
This usually entails together with the intermediate certificates together with the end-entity certificates. You should utilize on-line instruments (like SSL Labs’ SSL Server Check) to examine your certificates chain and establish any lacking hyperlinks.
- Answer: Be sure that the whole certificates chain is appropriately put in on the server the place the certificates is getting used.
- Hostname Mismatch: The certificates should be issued for the right area or subdomain that you simply’re attempting to entry. If the hostname within the certificates does not match the handle you are utilizing, the system will flag it as untrusted.
- Answer: Confirm that the certificates is issued for the right area or subdomain. When you’re utilizing a wildcard certificates (*.instance.com), guarantee it covers the particular subdomain you are accessing.
If not, you may must receive a certificates particularly for that subdomain.
- Answer: Confirm that the certificates is issued for the right area or subdomain. When you’re utilizing a wildcard certificates (*.instance.com), guarantee it covers the particular subdomain you are accessing.
Incorrect Certificates Codecs
Android helps numerous certificates codecs, however utilizing the fallacious one can result in set up failures. The commonest codecs are PEM (.pem, .crt, .cer) and PKCS#12 (.p12, .pfx). Understanding the variations and how one can convert between them is important.
- PEM Format (.pem, .crt, .cer): This can be a text-based format that usually incorporates the certificates and, typically, the personal key. It is the commonest format and infrequently used for particular person certificates or certificates chains.
- Downside: Trying to import a PEM-formatted certificates when the system expects a distinct format.
- Answer: Convert the PEM file to the suitable format on your system. For example, in the event you want a PKCS#12 file, you should utilize OpenSSL.
OpenSSL pkcs12 -export -in certificates.pem -inkey privatekey.pem -out certificates.p12
- PKCS#12 Format (.p12, .pfx): This can be a binary format that may retailer the certificates, its related personal key, and intermediate certificates, all in a single file. It is usually used for importing certificates and keys into gadgets or purposes.
- Downside: Utilizing the fallacious password when importing a PKCS#12 file. PKCS#12 information are normally password-protected for safety.
- Answer: Double-check the password you supplied when exporting the PKCS#12 file. When you’ve forgotten the password, you might must regenerate the certificates and personal key.
- Unsupported Certificates Sort: Android might not assist sure certificates sorts, akin to these with uncommon key lengths or cryptographic algorithms.
- Downside: The certificates makes use of a cryptographic algorithm or key size not supported by the Android system.
- Answer: Make sure the certificates makes use of a supported algorithm and key size. Fashionable Android variations usually assist SHA-256 and better with key lengths like 2048 bits or larger. You might must reissue the certificates utilizing a supported configuration.
Certificates Codecs and Compatibility

Ah, the fantastic world of digital certificates! Similar to selecting the best outfit for a elaborate gala, choosing the right certificates format is essential on your Android system to play properly with SSL/TLS secured connections. Getting this proper is the distinction between clean crusing and a irritating sea of error messages. Let’s unravel the thriller of certificates codecs and the way to make sure your Android system speaks the identical language as your safe servers.
Supported Certificates Codecs
Android, in its infinite knowledge (and with a bit of assist from the requirements our bodies), helps just a few key certificates codecs. Understanding these is step one in your journey to SSL/TLS enlightenment. Right here’s a breakdown of the standard suspects:
- .PEM (Privateness Enhanced Mail): That is maybe probably the most versatile format. It is basically a container that may maintain the certificates itself, the personal key, and even the whole certificates chain (the certificates, any intermediate certificates, and the basis certificates). PEM information are simply identifiable as a result of they begin with “—–BEGIN CERTIFICATE—–” and finish with “—–END CERTIFICATE—–” (or comparable headers/footers for personal keys). Consider it because the Swiss Military knife of certificates codecs.
- .CRT (Certificates): Typically a PEM file, however typically simply the certificates knowledge itself, encoded in a format like Base64. A .CRT file usually incorporates the general public key and different certificates particulars. It is generally used to retailer the server’s certificates.
- .CER (Certificates): Just like .CRT, the .CER extension normally signifies a certificates file, usually encoded in DER (Distinguished Encoding Guidelines) format, which is a binary format. You may discover it holding a single certificates or a whole certificates chain.
- .DER (Distinguished Encoding Guidelines): That is the binary encoding of the certificates. It’s not human-readable like PEM. Whereas in a roundabout way put in, Android can perceive certificates on this format, particularly when they’re a part of a PKCS#12 file.
- .PKCS#12 (.PFX or .P12): This format is a container for the certificates and the personal key, usually password-protected. It’s helpful when you could import each the certificates and the personal key into your Android system (e.g., for shopper authentication). This is sort of a safe bundle, safeguarding each the private and non-private parts.
Changing Between Certificates Codecs
Typically, you’ll end up with a certificates in a single format and your Android system craving one other. Worry not! Conversion instruments are available. These instruments are your trusty sidekicks within the battle in opposition to format incompatibility.
Right here’s how one can usually convert between codecs utilizing OpenSSL, a robust command-line instrument (usually accessible on Linux, macOS, and Home windows through instruments like Cygwin or WSL):
- Changing .PEM to .DER:
- Changing .DER to .PEM:
- Changing .PFX/.P12 to .PEM:
- Changing .PEM to .PFX/.P12:
openssl x509 -in certificates.pem -out certificates.der -outform DER
This command takes a .PEM file as enter and outputs a .DER file.
openssl x509 -in certificates.der -inform DER -out certificates.pem -outform PEM
This converts a .DER file to .PEM.
openssl pkcs12 -in certificates.p12 -out certificates.pem -nodes
You will possible be prompted for the password of the .p12 file. The -nodes possibility prevents the personal key from being encrypted within the output .PEM file (use this fastidiously; encrypt the important thing if safety is paramount).
openssl pkcs12 -export -in certificates.pem -inkey personal.key -out certificates.p12
This assumes you’ve gotten each the certificates (certificates.pem) and the personal key (personal.key). You’ll be prompted to set a password for the .p12 file.
Notice: These instructions assume you’ve gotten OpenSSL put in and configured in your system. Additionally, all the time deal with personal keys with excessive care. Hold them safe, and by no means share them publicly.
Verifying Certificates Format and Compatibility
Earlier than you go forward and set up a certificates, it is sensible to double-check its format and ensure your Android system will settle for it. Consider it as a high quality management examine earlier than the large day. There are just a few methods to perform this.
- Checking the File Extension: That is the only examine. If the file ends in .PEM, .CRT, or .CER, you are possible coping with a certificates file. .PFX or .P12 suggests a PKCS#12 file containing each the certificates and personal key.
- Utilizing a Textual content Editor: Open the certificates file in a textual content editor. When you see “—–BEGIN CERTIFICATE—–” and “—–END CERTIFICATE—–”, it is a PEM file. This fast inspection can prevent plenty of complications.
- Utilizing OpenSSL (Once more!): OpenSSL also can provide help to examine the certificates’s contents and format.
- Android System Compatibility Testing: The final word take a look at is, in fact, to strive putting in the certificates in your Android system. If it installs with out errors, you are golden! If not, you may must convert the format.
openssl x509 -in certificates.pem -text -noout
This command shows the certificates particulars in a human-readable format, together with the issuer, topic, validity interval, and public key. It really works with PEM, CRT, and CER information.
Instance: As an instance you are attempting to put in a certificates for a web site. You obtain a file known as “web site.crt”. You open it in a textual content editor and see the “BEGIN CERTIFICATE” and “END CERTIFICATE” markers. This implies it is a PEM-formatted certificates, which is extremely appropriate with Android. You then attempt to set up it in your Android system, and it really works completely.
Success!
Safety Concerns and Greatest Practices
Navigating the digital panorama in your Android system calls for a eager understanding of safety protocols, particularly when coping with SSL certificates. These certificates are the digital keys that unlock safe communication channels, however they may also be a degree of vulnerability if dealt with carelessly. This part delves into the essential features of safe certificates administration, making certain your knowledge stays shielded from prying eyes.
Significance of Reliable Certificates Sources
The bedrock of safe SSL certificates set up lies within the trustworthiness of the supply. Consider it like this: You would not settle for a key to your home from a stranger, would you? Equally, you need to solely set up certificates from entities you genuinely belief. Certificates from untrusted sources pose important dangers, probably permitting malicious actors to intercept your knowledge, impersonate respectable web sites, or launch refined assaults.
Safe Storage and Administration of SSL Certificates
Defending your SSL certificates is akin to safeguarding your digital identification. Implementing strong storage and administration practices is essential to mitigate potential threats. This entails a multi-layered method, encompassing safe storage, common backups, and managed entry. Think about the next:
- Password Safety: All the time password-protect your certificates information. A robust, distinctive password is the primary line of protection. Consider it because the lock in your digital vault.
- Safe Storage Location: Retailer certificates in a safe location in your system. This may contain utilizing a devoted certificates retailer or a password-protected file supervisor. Keep away from storing them in simply accessible folders.
- Common Backups: Create common backups of your certificates. Within the occasion of knowledge loss or system failure, you’ll be able to restore your certificates and preserve safe connections.
- Entry Management: Restrict entry to your certificates. Solely licensed personnel ought to be capable of view, modify, or delete them. This minimizes the chance of unauthorized entry and potential misuse.
- System Encryption: Allow system encryption. This encrypts all knowledge in your system, together with certificates, defending them even when your system is misplaced or stolen.
Potential Dangers of Putting in Untrusted Certificates
Putting in certificates from unknown or untrusted sources opens the door to a number of safety vulnerabilities. It is like inviting a wolf in sheep’s clothes into your digital ecosystem. These dangers can have extreme penalties, starting from knowledge breaches to identification theft. Among the main risks embody:
- Man-in-the-Center Assaults (MitM): Untrusted certificates can be utilized to carry out MitM assaults. This permits attackers to intercept and decrypt your communications, stealing delicate info akin to usernames, passwords, and monetary knowledge. Think about somebody eavesdropping in your conversations and stealing your secrets and techniques.
- Phishing Assaults: Malicious actors can use untrusted certificates to create pretend web sites that seem respectable. They will then trick you into coming into your credentials, resulting in phishing assaults. That is like receiving a pretend electronic mail out of your financial institution, designed to steal your account particulars.
- Malware Distribution: Untrusted certificates can be utilized to signal malicious software program, making it seem reliable. Once you set up this software program, it could possibly compromise your system and steal your knowledge. That is akin to accepting a present from a stranger that incorporates a hidden, harmful shock.
- Knowledge Breaches: Compromised certificates can result in knowledge breaches. Attackers can exploit vulnerabilities to achieve entry to your knowledge, resulting in the publicity of delicate info.
Greatest Practices for Safe Certificates Administration
Implementing these greatest practices will provide help to to create a sturdy safety posture and defend your knowledge. This desk encapsulates key methods for safe certificates administration:
| Sort of Greatest Apply | Description | Advantages |
|---|---|---|
| Confirm Certificates Authority (CA) | All the time confirm the Certificates Authority (CA) that issued the certificates. Make sure the CA is a trusted and respected entity. Verify the certificates particulars for the issuer’s identify and confirm it in opposition to an inventory of recognized, trusted CAs. | Reduces the chance of utilizing certificates from fraudulent or compromised CAs, making certain that the certificates originates from a respectable supply. |
| Use Robust Passwords | Defend certificates information with sturdy, distinctive passwords. Keep away from utilizing simply guessable passwords, akin to private info or widespread phrases. Think about using a password supervisor to generate and retailer sturdy passwords. | Prevents unauthorized entry to certificates information, even when the system or storage location is compromised. Robust passwords are the primary line of protection in opposition to brute-force assaults. |
| Repeatedly Replace Certificates | Guarantee certificates are commonly up to date. Certificates have an expiration date. When a certificates expires, safe connections will likely be interrupted. Set reminders to resume certificates earlier than they expire. | Maintains the safety of your connections. Expired certificates can disrupt companies and expose your knowledge to dangers. Common updates additionally embody the newest safety enhancements. |
| Monitor Certificates Utilization | Repeatedly monitor certificates utilization. Assessment logs to establish any unauthorized entry or uncommon exercise. Arrange alerts to inform you of any suspicious conduct, akin to makes an attempt to entry certificates information. | Helps detect and reply to potential safety breaches. Early detection permits you to take fast motion, minimizing the influence of any safety incidents. |
Certificates Revocation and Renewal
Certificates are like digital passports, vouching for the identification of internet sites and making certain safe connections. However typically, these digital passports get misplaced, stolen, or just expire. That is the place certificates revocation and renewal come into play, essential features of sustaining a safe looking expertise in your Android system.
Certificates Revocation: Understanding the Dangers
Certificates revocation is the method of invalidating a beforehand issued SSL certificates earlier than its expiration date. This occurs when a certificates is compromised, the personal secret is leaked, or the certificates authority (CA) that issued the certificates deems it untrustworthy. Revocation prevents malicious actors from utilizing the compromised certificates to impersonate respectable web sites and intercept your knowledge. The influence on Android gadgets will be important, probably blocking entry to web sites or apps that depend on the revoked certificates.
If a certificates is revoked, your system will show an error message, warning you concerning the potential safety danger.To grasp the implications, think about you are attempting to go to your financial institution’s web site. If the financial institution’s certificates is revoked, your Android system will refuse to attach, displaying an error. It is because your system trusts the CA that issued the certificates, however that CA has now declared the certificates invalid.
Checking Certificates Revocation Standing
It is vital to confirm if a certificates has been revoked. Whereas Android handles revocation checks mechanically in lots of instances, manually verifying can present an additional layer of safety.
- Utilizing the Browser: Most Android browsers, like Chrome and Firefox, carry out revocation checks mechanically. Once you go to a web site, the browser checks the certificates’s standing. If the certificates is revoked, the browser will show a warning and stop you from accessing the location.
- Certificates Transparency Logs: Certificates Transparency (CT) logs are public, append-only logs of issued SSL/TLS certificates. You should utilize on-line instruments or browser extensions to examine if a certificates is current in CT logs and whether or not it has been revoked. This technique affords a extra detailed view of the certificates’s standing.
- Certificates Authority’s CRL/OCSP: Certificates Authorities (CAs) preserve Certificates Revocation Lists (CRLs) or use On-line Certificates Standing Protocol (OCSP) to supply real-time revocation info. You should utilize on-line instruments or seek the advice of the CA’s documentation to examine a certificates’s revocation standing.
Checking for revocation is like double-checking your lock earlier than you permit the home; it’s an additional step to make sure your safety.
Renewing SSL Certificates on Android
Renewing an SSL certificates is important to sustaining safe connections, particularly when the certificates nears its expiration date. Whereas Android customers usually do not instantly renew certificates for web sites (that is the web site proprietor’s accountability), they want to pay attention to the method and the way it impacts their looking expertise. The method entails producing a brand new certificates and putting in it on the net server.
When the certificates is renewed, the web site proprietor installs the brand new certificates on the server, and the Android system will mechanically belief it, assuming the brand new certificates is issued by a trusted CA.The method usually unfolds as follows:
- Web site Proprietor’s Motion: The web site proprietor generates a brand new certificates signing request (CSR) and submits it to a Certificates Authority (CA).
- Certificates Issuance: The CA verifies the web site proprietor’s identification and points a brand new SSL certificates.
- Certificates Set up: The web site proprietor installs the brand new certificates on the net server.
- Android System’s Function: When an Android system connects to the web site after the certificates renewal, the system verifies the brand new certificates’s validity, together with its expiration date, and trusts the connection if the certificates is issued by a trusted CA.
Think about your favourite on-line retailer renewing its safety certificates. Once you subsequent go to, your Android system mechanically verifies the brand new certificates, making certain a continued safe purchasing expertise. The method is seamless, so long as the web site proprietor renews the certificates and installs it appropriately.
Visible Guides and Illustrations
Let’s face it: typically, phrases simply aren’t sufficient. When coping with technical processes, an image really is value a thousand keystrokes. This part dives into the visible aids that make understanding SSL certificates set up on Android a breeze, making certain you’ll be able to confidently navigate the method. These illustrations are designed to be clear, concise, and simple to observe, reworking advanced steps into a simple visible journey.
Importing an SSL Certificates into Android Settings
The Android settings menu can typically really feel like a labyrinth. That is why a transparent visible information is important.Think about an illustration depicting the method of importing an SSL certificates throughout the Android settings menu. The illustration ought to include a sequence of sequential panels, every representing a step within the course of.* Panel 1: The Android Settings Icon. This panel reveals the enduring Android settings gear icon, prominently displayed on a typical Android residence display screen.
A small arrow factors from the house display screen to the settings icon, emphasizing the place to start.* Panel 2: Navigating to Safety Settings. This panel zooms in on the settings menu. A visible illustration of the menu, with an inventory of choices, is proven. A highlighted rectangle encompasses the “Safety” or “Safety & Location” possibility (the particular wording might range barely relying on the Android model).
An arrow factors from the settings menu to this feature.* Panel 3: Accessing Certificates Settings. This panel reveals the “Safety” menu. Inside this menu, a piece labeled “Encryption” or “Credentials” (once more, the particular identify can range) is displayed. Inside this part, the “Certificates administration” or “Trusted credentials” possibility is highlighted with an arrow pointing to it.* Panel 4: Importing the Certificates. This panel zooms into the certificates administration settings.
Right here, a button labeled “Set up a certificates” or the same phrase, maybe represented by a plus signal icon or an “Import” button, is prominently displayed. An arrow signifies the consumer’s motion to faucet or click on this button.* Panel 5: File Choice. This panel reveals a file choice dialog, typical of Android. It shows an inventory of file managers or storage places (inside storage, SD card, and many others.).
The illustration ought to present a consumer deciding on a selected file supervisor (e.g., “Recordsdata by Google”) and navigating to the placement the place the certificates file (e.g., a `.crt` or `.pem` file) is saved. A small arrow signifies the choice and file navigation.* Panel 6: Certificates Particulars and Affirmation. This panel reveals the certificates particulars. This contains the certificates’s identify, the issuing authority, and validity dates.
It must also embody a button labeled “OK” or “Set up” to verify the set up. A checkmark icon may seem subsequent to the certificates identify after set up.This complete illustration makes use of clear icons, daring textual content labels, and directional arrows to information the consumer by way of every step, making certain a user-friendly and simply comprehensible visible illustration of the certificates import course of.
Putting in a Certificates through File Supervisor, Set up ssl certificates on android
Putting in a certificates by way of a file supervisor affords one other handy technique, particularly for customers preferring a extra hands-on method.An illustration can present the steps for putting in a certificates through a file supervisor, together with icons and UI components.* Panel 1: The File Supervisor Icon. The illustration begins with an outline of a typical Android residence display screen, displaying a file supervisor app icon (e.g., “Recordsdata,” “My Recordsdata,” or comparable).
An arrow factors from the house display screen to the file supervisor icon.* Panel 2: Finding the Certificates File. The illustration zooms into the file supervisor interface. The consumer is proven navigating the file system, deciding on the placement the place the certificates file (e.g., `.crt`, `.pem`, or `.der`) is saved. A visible illustration of a file folder construction, with clearly labeled folders and file names, is included.* Panel 3: Choosing the Certificates File. The illustration highlights the certificates file throughout the file supervisor.
The file identify is proven with a transparent visible cue, akin to a distinct coloration background or a checkmark icon, to point choice. An arrow factors from the file to the following step.* Panel 4: The “Open With” Menu. When the certificates file is chosen, the illustration reveals the “Open with” or “How do you wish to open this?” immediate that usually seems in Android.
Choices akin to “Certificates installer,” “Set up certificates,” or comparable are displayed.* Panel 5: Certificates Set up Immediate. The illustration depicts the Android system’s certificates set up immediate. This may embody the certificates’s identify, issuing authority, and a immediate to call the certificates and select the certificates’s function (e.g., “VPN and apps” or “Wi-Fi”). Fields for coming into the certificates identify and deciding on the utilization are clearly proven.* Panel 6: Affirmation and Success. The ultimate panel reveals the certificates efficiently put in, usually represented by a notification or a change within the consumer interface, such because the certificates now showing within the “Trusted credentials” part of the Android settings.
A checkmark subsequent to the certificates signifies the profitable set up.This illustration makes use of recognizable UI components, akin to file icons, file supervisor navigation, and system prompts, to supply a transparent and intuitive information to putting in a certificates through a file supervisor.
Trusted vs. Untrusted Certificates in a Net Browser
Understanding the visible cues that distinguish a trusted from an untrusted certificates is essential for sustaining on-line safety.An illustration demonstrates the distinction between a trusted and an untrusted certificates in an Android net browser, with clear visible cues.* Panel 1: The Safe Connection Icon (Trusted). The primary panel reveals an internet browser’s handle bar with a web site handle. A padlock icon (🔒) is prominently exhibited to the left of the web site handle (e.g., `https://instance.com`).
The padlock is coloured inexperienced and is closed. This means a safe reference to a trusted certificates. A small label close to the padlock says, “Connection is safe.”* Panel 2: The Safe Connection Particulars (Trusted). The illustration reveals what occurs when a consumer faucets the padlock icon. A pop-up or a small informational panel seems, indicating the connection is safe. It contains info akin to the web site’s identification (the area identify), the certificates issuer (e.g., “Let’s Encrypt”), and the validity interval.* Panel 3: The Warning Icon (Untrusted). The following panel reveals the identical net browser handle bar, however now, as a substitute of a inexperienced padlock, a warning icon is displayed.
This icon could possibly be an open padlock (🔓), a crimson padlock (🔒), or a triangle with an exclamation level (⚠). The handle bar may additionally show a message akin to “Not safe” or “Your connection is just not personal.”* Panel 4: The Warning Particulars (Untrusted). The illustration reveals what occurs when the consumer faucets the warning icon. A pop-up or informational panel seems, explaining that the connection is just not personal.
It states the explanation for the untrusted certificates, akin to “This web site’s safety certificates is just not trusted,” “The certificates is expired,” or “The certificates is just not legitimate for this website.” The panel may supply choices to view the certificates particulars (for superior customers) or to proceed to the web site (with a warning that the connection is just not safe).* Panel 5: Extra Warning Element (Untrusted). This panel additional reveals the small print concerning the certificates drawback.
It could point out the certificates issuer is unknown or that the certificates has been revoked. A distinguished warning message is included to alert the consumer of potential dangers.This illustration makes use of clear and universally understood icons, coloration coding (inexperienced for trusted, crimson/yellow for untrusted), and concise textual content labels to obviously exhibit the visible variations between a trusted and an untrusted certificates, empowering customers to make knowledgeable selections about their on-line safety.